Unlock the Secret: What Does zpv bsf bxftpnf Really Mean?
Decipher the Code zpv bsf bxftpnf, a substitution cypher whereby a given number shifts the alphabet’s letters.
Hidden messages have always fascinated people in the fields of codes, puzzles, and cryptography. Deciphering these messages can make one feel successful as well as challenged intellectually. At first, it could seem to be a haphazard collection of letters, but with the correct approach, you can expose the underlying significance.
The technique used to decode this code will be discussed in this paper,r together with a broad knowledge of cryptographic codes and their uses in other spheres.
We will also review useful cases and address some often asked questions (FAQs) on codes and cryptography.
What Does Decipher the Code zpv bsf bxftpnf Mean?
You are not alone if you have been intrigued by this unusual-looking term. The good news is that everyone can decode this basic Decipher the Code zpv bsf bxftpnf—not some sophisticated hacking code. Deciphered differently, the phrase conveys a favourable message:
“YOU ARE AWESOME”
But how does this metamorphosis take place? It’s all about moving letters in a particular manner—a method applied in a well-known kind of code known as the Caesar cypher. Originally looking jumbled, the letters advance in the alphabet and seem disorganised. Once you reverse them, though, the words start becoming clear. It resembles discovering a secret!
Knowing what the message says, let’s examine more closely how you might decode it personally.
How does the Cypher Behind Decipher the Code zpv bsf bxftpnf Work?
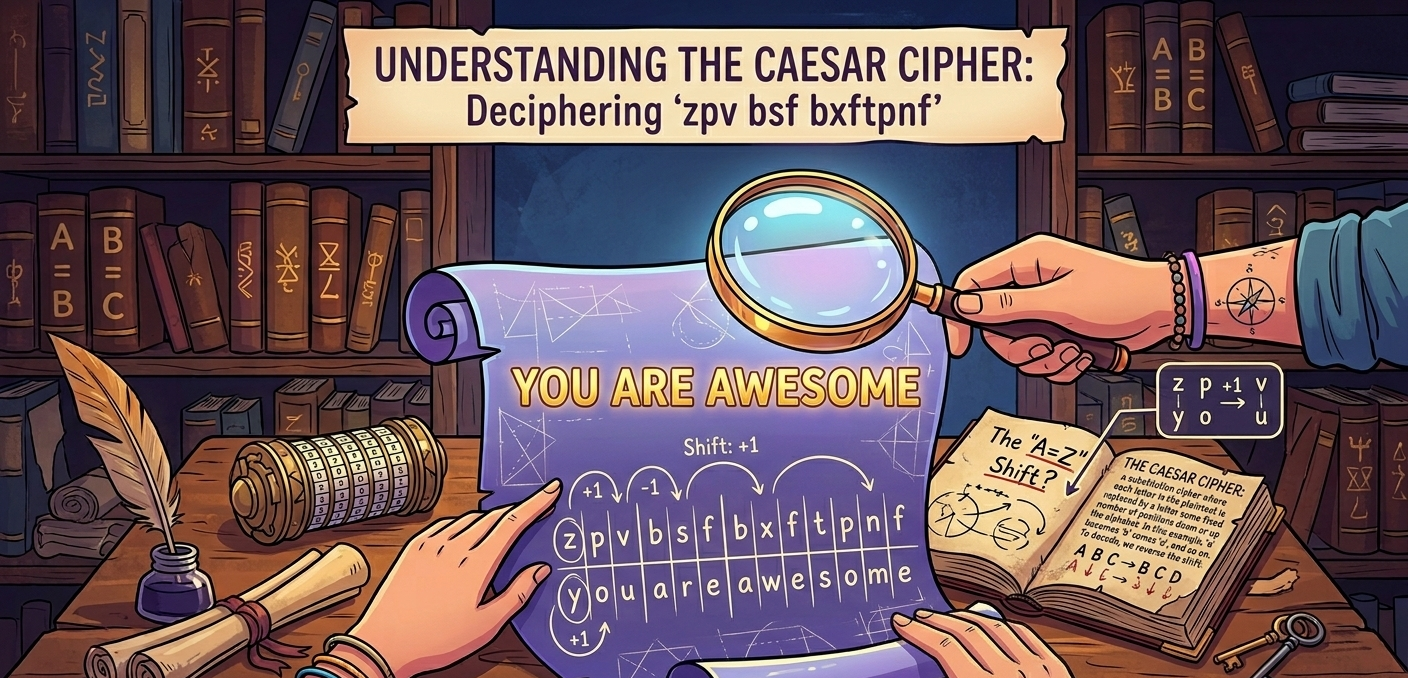
Caesar cypher with a 1-shift code: “ZPV BSF BXFTPNF”. Every letter in the original message was therefore advanced one place in the alphabet. Let’s try this:
- Z → Y
- P → O
- V → U
That gives us “YOU.” Now, let’s do the next word:
- B → A
- S → R
- F → E
Now we have “ARE.” Finally, let’s decipher the last word:
- B → A
- X → W
- F → E
- T → S
- P → O
- N → M
- F → E
Now we have “AWESOME.” All taken together, you arrive at “YOU ARE AWESOME.” Fantastic, right?
The History Behind Decipher the Code zpv bsf bxftpnf
Secret codes have been applied for thousands of years by people. Secret communications were applied in battle, politics, and even love letters in the past! Named for Julius Caesar, the Caesar cypher is one of the most well-known instances. Using this approach, he sent secret signals to his troops so that competitors would not grasp them.
Cyphers are based on the straightforward concept of predictable letter changes that only those who know the method can read. More sophisticated cyphers were developed over time, which produced today’s encryption techniques applied for internet security and privacy. Still, simple cyphers like these remain entertaining for use in puzzles, games, and brain teasers, even with contemporary technologies! Knowing how to break these codes can help you feel like a detective,e whether your escape room adventure is simple fun with friends or something more. Let us dissect just how the Caesar cypher operates.
Why Decipher the Code zpv bsf bxftpnf Are Used
-
The History of Cryptography
Cryptography is long and rich in history. Encoding and decoding communications have roots thousands of years ago. Ancient societies, such as the Greeks and Egyptians, established simple cyphers to protect their private secrets. Julius Caesar reportedly used the Caesar cypher, the most well-known early example, to secure his military communications. The discipline of cryptography grew with the rise of modern computing, leading to the creation of increasingly complex methods over time.
-
Modern Applications for Codes and Cyphers
In the digital era, communications security depends much on cryptography. Every day, people employ cyphers to ensure privacy and security, whether it’s for encrypting important government data, safeguarding credit card information, or protecting passwords. Although the underlying ideas remain the same, modern encryption methods, including AES (Advanced Encryption Standard), are far more complicated and safe than the Caesar cypher.
Uses of Decoding in Actual Life
-
Encryption in Security
Data security is among the most critical applications for cryptography. Encryption methods guard your personal data from hackers intercepting eit very time you log into your email account or make an online purchase. The internet would be a perilous venue for private data without cryptography. When you access a website running HTTPS (HyperText Transfer Protocol Secure), for example, SSL/TLS encrypts the interaction between your browser and the server. This protocol guarantees that third parties cannot view any material you share, including passwords or credit card information.
-
Games and Entertainment: Problems
Apart from safeguarding private data, cryptography finds uses in entertainment—especially in games and riddles. For example, many escape room tasks use cyphers, while puzzles in novels, movies, and even video games often incorporate cryptographic codes to conceal clues or messages. Deciphering messages via games and puzzles gives enthusiasts of cryptography both enjoyment and a mental workout, improving logical thinking and problem-solving ability.
The Bottom Line
Finally, the message “Decipher the Code zpv bsf bxftpnf” is a perfect illustration of a basic cypher for which the Caesar cypher approach provides quick decoding. This decryption approach, despite its simplicity, opened the path for contemporary encryption technologies that are vital in today’s digital environment of today.
Whether you’re working on crucial encryption techniques or deciphering texts for pleasure, cryptography remains a necessary component of everyday life. It began as a simple shift cypher and has evolved into incredibly complex algorithms that protect everything from our personal data to national security.
FAQs
-
The Caesar cypher is what?
A Caesar cypher, a type of substitution cypher, shifts each letter in the plaintext by a predetermined number of alphabetical positions. Named for Julius Caesar, who used it to guard military communications, the technique is among the simplest and earliest encryption methods.
-
Decipher a Caesar cypher here?
Decrypting the encryption process will help you to decode a Caesar cypher. You move each letter of the cypher text backwards by the same amount to expose the original message if the text was moved forward by a given number.
-
Are there any other common types of cyphers?
Apart from the Caesar cypher, other widely used cyphers are the Vigenère cypher, which varies the shifts applied to every letter using a keyword, and the substitution cypher, in which each letter is substituted by another letter.